The question of security is paramount in the crypto world. As digital assets continue to gain popularity, so does the need for secure storage solutions. This has led to the rise of hardware wallets and cold wallets, often touted as the safest options for storing your precious digital currencies. But how secure are they really? Can hardware wallets be hacked? Can cold wallets be hacked? These are the questions that every crypto investor, both seasoned and novice, is asking.
Hardware wallets, often referred to as ‘cold wallets’ due to their offline nature, have become the go-to choice for many. They offer a level of security that online ‘hot wallets’ simply can’t match. But like any technology, they are not impervious to threats. From phishing scams to physical tampering, hardware wallets have their vulnerabilities.
| Topic | Summary |
|---|---|
| 🔒 Hardware Wallets | Hardware wallets are a type of crypto wallet that store private keys offline, often referred to as “cold wallets”. They are typically USB sticks or similar devices that come preloaded with software to safely store cryptocurrencies offline. Examples include Ledger Nano X, Trezor T, KeepKey, CoolWallet, and BitBox. |
| 🌐 Cold Wallets vs Hot Wallets | Cold wallets, like hardware wallets, store private keys offline, making them less vulnerable to online hacking attempts. In contrast, hot wallets are software or online accounts where cryptos are stored, making them more vulnerable as private keys are generated and stored on the same device used to access the account. |
| ❓ Are Hardware Wallets Unhackable? | While hardware wallets are safer than hot wallets due to their offline nature, they are not completely safe. They can be susceptible to phishing scams, physical tampering, and counterfeit hardware wallets. It’s important to verify the device before use and never share private keys without verifying the recipient’s identity. |
| 🛡️ Protecting Your Wallet | Protection of hardware wallets primarily involves proper management of the private key and seed phrase. It’s recommended to never store the private key or seed phrase online or in a photograph. Instead, make multiple handwritten copies or engrave them onto metal plates for water and fire resistance. |
| 🎯 Hardware Wallet Security | Hardware wallets are generally secure, with most crypto losses due to owner recklessness rather than device failure. Rules for securing hardware wallets include never sharing private keys, avoiding clicking on links in emails or IM messages, carefully storing the wallet seed, considering multi-signature cold storage, and using a 25th passphrase for added protection. |
| 💥 Hacking a Hardware Wallet | Hacking hardware wallets can be done through various methods, all of which require physical access to the wallet. These methods include power glitching (a physical attack), side-channel attacks (through emitted information), and software attacks. |
| 🔄 How Hardware Wallets Work | Hardware wallets work by storing private keys offline. Different brands use different approaches. For example, Ledger stores the cryptographic seed in the Secure Element chip, while Trezor stores it in the general-purpose microcontroller’s flash memory. |
What you'll learn 👉
Can Hardware Wallets Be Hacked?
A hardware wallet is a type of crypto wallet that stores your private keys (and consequently your coins) offline or in ‘cold storage, meaning that it cannot be accessed via an internet connection. They’re commonly referred to as “cold wallets” since they store your coins without being connected to the internet.
The most popular form of a hardware wallet is a USB stick, which is plugged directly into a computer. Although newer alternative wallets like Coolwallet Pro are coming in a shape of a credit card, Ngrave looks like a small box, etc.
These devices are designed to look like flash drives and come preloaded with software that allows you to safely store your cryptos offline.
There are many different types of hardware wallets out there, each offering varying levels of security. Some offer better protection against malware attacks, while others provide additional features such as multi-signature functionality.
Some examples of hardware wallets include Ledger Nano X and S (and more recently Nano S Plus), Trezor T, KeepKey, CoolWallet, Ellipal, and BitBox.
However, just because a hardware wallet is more secure than a regular software wallet doesn’t mean that it is completely safe. There are still some things that could go wrong.
Why Hardware Wallets (or Cold Wallets) are Superior to Hot Wallets?
The term “hot wallet” refers to software and online accounts where people store their cryptos. These include exchanges like Coinbase, Binance, and Kraken or software programs or apps such as Exodus, Coinomi, Atomic Wallet, etc.
Hot wallets typically use software running on a desktop or laptop computer, smartphone, or tablet. This means that your private keys are generated and stored in memory on the same device you’re using to access your account.
This makes hot wallets inherently vulnerable to hacking because if someone gets hold of your device, they can steal your funds. Of course, a much more common way hackers use to gain access to your account is via the internet.
A cold wallet is a different type of storage solution altogether. A hardware wallet, for example, generates and stores your private keys offline. This removes the risk of losing your coins if your device is lost or damaged.
Hardware wallets are built specifically to keep your money safe. You can think of them as airtight safes that lock away your digital assets.
Are Hardware Wallets Unhackable?
Hardware wallets are designed to store crypto keys offline while remaining unhackable or susceptible to malware. However, there are risks involved with these wallets as well. In fact, there are several different types of attacks that could compromise the private keys of your hardware wallet.
Phishing scams are one type of attack that attempts to trick you into handing over your private keys by sending malicious emails that look like they come from popular sites such as Coinbase or Bitfinex. Once you enter your credentials, the attacker gains access to your funds.
Another type of attack involves hackers physically tampering with your hardware wallet.
There have even been cases of counterfeit hardware wallets being shipped to unsuspecting customers. These fake wallets contain malware that allows attackers to steal private keys and drain your accounts.
Always make sure that your device is genuine before opening it up. Also, never give out your private keys to anyone without verifying that person’s identity.
How to protect your wallet?
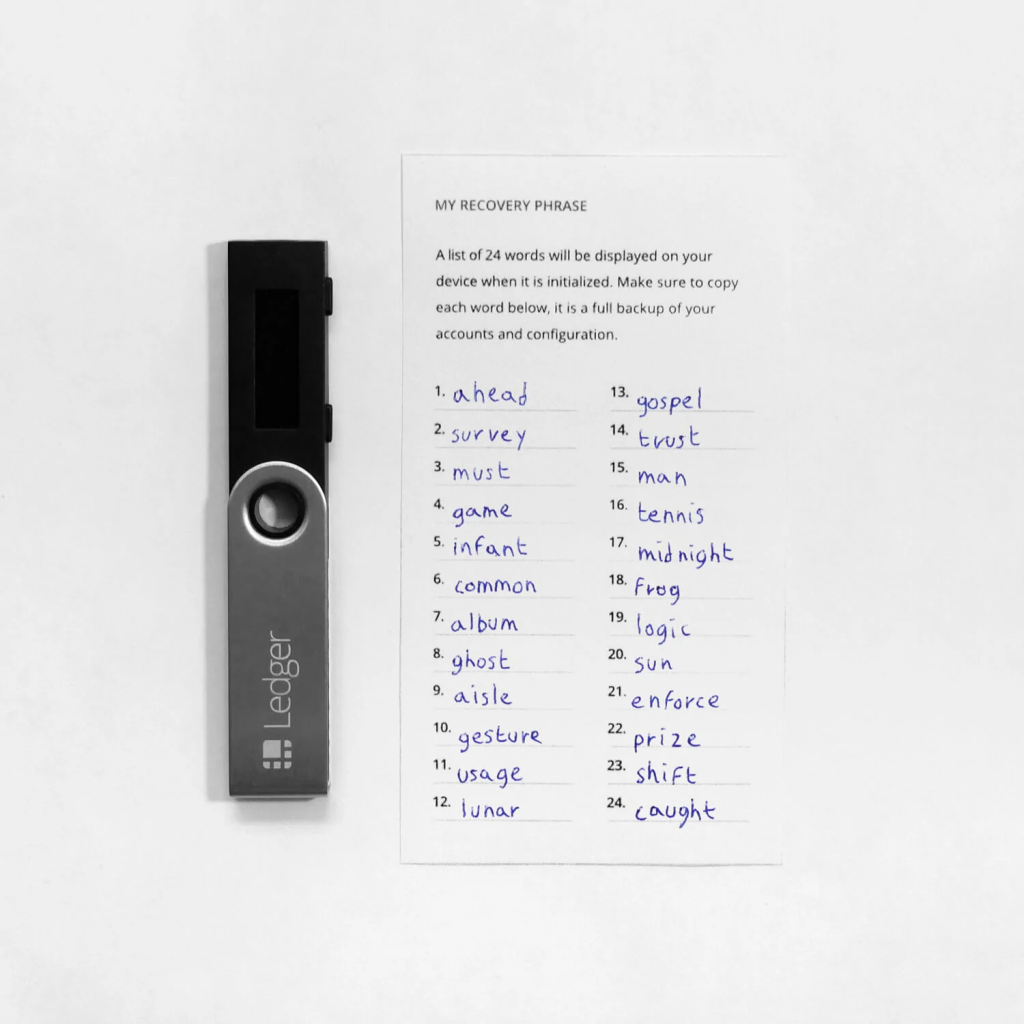
It all boils down to proper management of the private key and seed phrase. The device itself is less important. The seed phrase (12 or 24 words you get when you first start the hardware wallet) is your actual key to your crypto funds.

You should never put your private key into an online storage site like Dropbox or Google Drive because hackers could steal it and use it to take over your accounts.
You should never take a picture of your seed phrase either.
Make at least three copies by handwriting the words on pieces of paper. You can also use metal plates and engrave your seed phrases onto them (to make them water and fire-resistant).
You can split the seed phrases into multiple pieces and store each of the pieces with different persons/institutions. For example, leave part one with your parents, the second part with your friends, the third part can be stored in a safe deposit box in some bank, etc.
Why are hardware wallets safer?
A PIN and an optional passphrase safeguard your hardware wallet’s private keys. If a thief gets their hands on your hardware wallet, they’ll have a hard time getting your private keys. The keys cannot be stolen because they are not accessible via the internet. Hence the term “cold storage.”
How secure are hardware wallets?
In almost all situations, crypto losses via hardware wallets are due to the owner’s recklessnesses, not a device failure. These are the rules which help you to secure your hardware wallet:
Rule 1: Never tell anyone else about your private keys!
If you have a Coolwallet or Ledger with a Secure Element, you may rest easy. Your most sensitive information is stored in the Secure Element and cannot be accessed by anyone.
CoolWallet and Ledger have Secure Elements with the highest certification (CC EAL 5+). It saves sensitive data and works as a vault. It safeguards the private key at all times and never reveals it to anyone.
Rule 2: Never click on links you get in emails or IM messages!
As an internet user, you might have a situation where someone may try to steal your seed phrase in the following ways:
1) Phishing Malware – Clicking on the wrong link can lead you to a phony website that tricks you into entering your secret phrase or install hidden spyware that intercepts your confidential information.
2) Impersonation Phishing – Tens of thousands of scammers impersonate well-known crypto celebrities and firms.
Rule 3: Make sure you don’t misplace your Wallet Seed
It is critical to ensure that the wallet seed phrase is correct and that it is kept safe at all times. Don’t try to memorize it, store it in odd or risky places, or play smart games with it. Keep it in a dry and safe place, such as a steel wallet or a safe.
How to Hack a Hardware Wallet?
Hacking hardware wallets can be done in several different ways with one goal in mind — obtaining sensitive data like your PIN number or private keys. A hardware wallet can potentially be hacked by any one of the following methods (each of them requires physical access to the wallet by the hacker, which is less likely to happen – software wallets, on the other side, are hacked via the internet quite often):
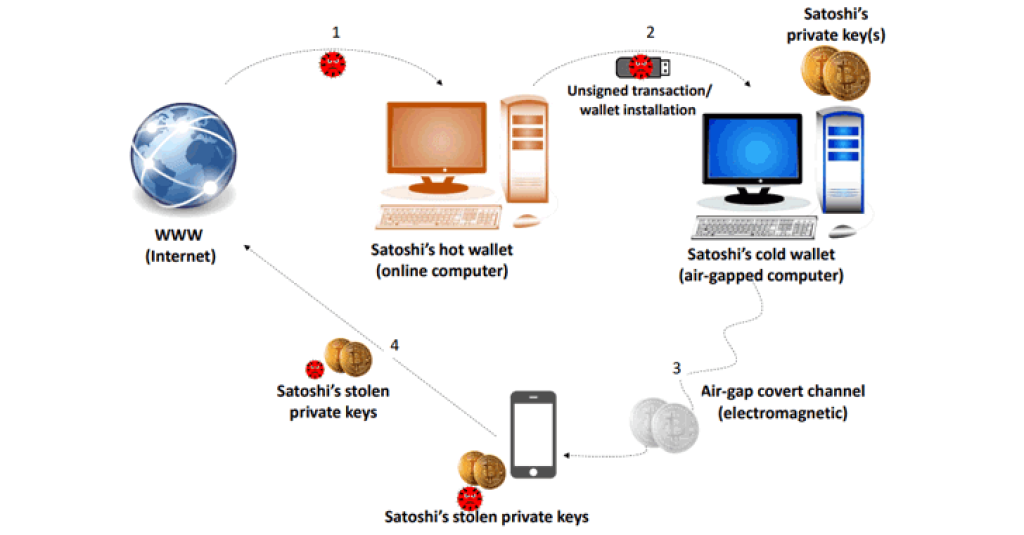
A physical attack: Power glitching
A power glitch causes a circuit board’s power source to briefly go out of order, causing the device to be temporarily confused by the shockwave. The resulting confusion exposes sensitive data to an attacker.
Hacking the microcontroller chip unlocks the info contained. A power glitch attack uses high voltage current bursts to leave a component exposed, providing access to raw data. From here, it’s easy to retrieve the device’s PIN code and private chip data.
Through emitted information: Side-channel attacks
A side-channel attack observes a hardware wallet’s transaction activity.
An oscilloscope is used to monitor a device’s power usage during a side-channel assault. You may see how each code impacts utilization by listening to the device’s noise and testing random PIN codes. Different PIN digit values leave a distinct footprint, making it simple to distinguish codes.
Each time a PIN is entered, a record is made of the amount of power used. A script that predicts PIN numbers is used in conjunction with the information to crack the code.
Getting the secrets with software: Breaking the hardware with a software attack
Once the hardware module is plugged into a computer, you interact with it in order to recover the software that runs on it. When you execute a script to look for the program in binary form in the device’s code, this happens. Reverse engineering is needed to get the information to a place where it can be understood because humans don’t understand binary code at all.
Using redacted software information, the goal is to uncover a vulnerability that can be exploited to gain control of the software and acquire data from it.
How do hardware cryptocurrency wallets work?
Offline storage is the primary benefit of hardware wallets. As a digital wallet that holds your crypto offline, they’re a good fit. Instead of being transferred to a third-party server, private keys are kept on the device itself. This prevents hackers from stealing your money.
Ledger’s approach: The cryptographic seed is stored in the Secure Element chip
Ledger’s device isn’t completely secure because of its cryptography chip. Although it’s difficult to attack a Secure Element and obtain a cryptographic seed, it’s easy to corrupt a general-purpose microcontroller and trick a hardware wallet into confirming an outsider’s transactions.
The device’s microcontroller can remap memory, changing the access address. Researchers used this functionality to modify Nano S firmware. This updated firmware could contain a malicious module that modifies outgoing addresses.
Side-channel attacks can affect Ledger Blue. Ledger Blue’s circuit board leaks RF signals when a PIN code is entered. Researchers created a machine-learning algorithm to recognize the signals 90% of the time.
Trezor’s approach: The cryptographic seed is stored in the general-purpose microcontroller’s flash memory
In the Trezor world, things are a little more unique. Everything in the device is controlled by a single microprocessor based on the ARM architecture, thus, there is no need for a separate Secure Element. On this chip, you’ll find anything from cryptographic data storage to control of your USB connection and so on.
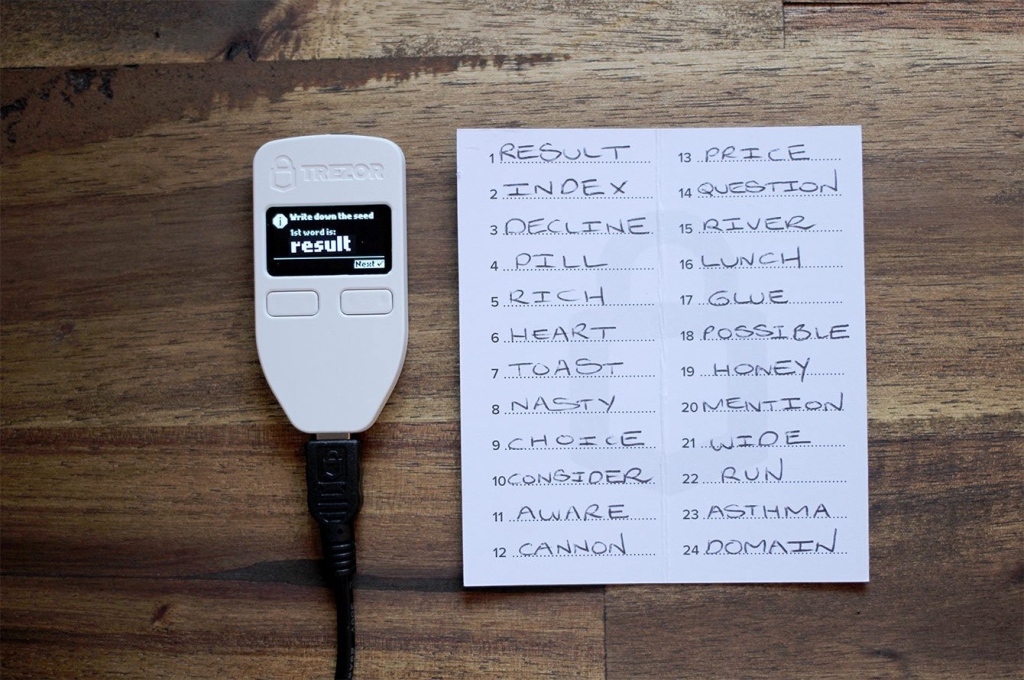
Voltage glitching, a hacking technique, was used to flip Trezor One’s chip state from “no access” to “partial access,” allowing them to read the chip’s RAM but not it’s flash storage. The result was a successful attack.
During the process of upgrading the firmware, the chip places the cryptographic seed in RAM to keep it safe while the flash is being overwritten. They were able to retrieve the entire contents of the memory in this method. The cryptographic seed was found in this dump unencrypted, in the form of a mnemonic phrase (meaning actual words instead of a random integer) that was easy to recognize.