Before we start with the subject, let’s take a look at the meaning of mnemonic. According to Wikipedia, a mnemonic device, or memory device, is any learning technique that aids information retention or retrieval (remembering) in the human memory. Mnemonics make use of elaborative encoding, retrieval cues, and imagery as specific tools to encode any given information in a way that allows for efficient storage and retrieval.
Mnemonics aid original information in becoming associated with something more accessible or meaningful – which, in turn, provides better retention of the information. Commonly encountered mnemonics are often used for lists and in auditory form, such as short poems, acronyms, or memorable phrases, but mnemonics can also be used for other types of information and in visual or kinesthetic forms.
Their use is based on the observation that the human mind more easily remembers spatial, personal, surprising, physical, sexual, humorous, or otherwise “relatable” information, rather than more abstract or impersonal forms of information.
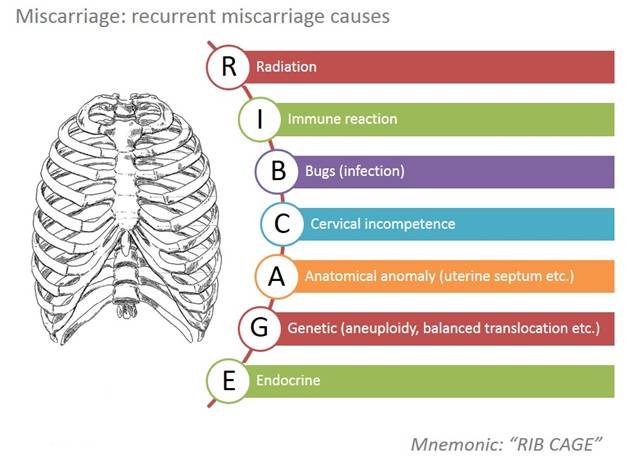
For instance, to remember the 10 organ systems of the human body, you can use a memorable phrase such as NICER DRUMS (Nervous, Integumentary, Circulatory, Endocrine, Respiratory, Digestive, Reproductive, Urinary, Muscular, and Skeletal).
What you'll learn 👉
Mnemonic Phrase
In the world of cryptocurrencies, mnemonic phrase, mnemonic recovery phrase or mnemonic seed is a list of words which store all the information needed to recover a Bitcoin wallet. Wallet software will typically generate a mnemonic backup phrase and instruct the user to write it down on paper. If the user’s computer breaks or their hard drive becomes corrupted, they can download the same wallet software again and use the paper backup to get their bitcoins back.
Anybody else who discovers the phrase can steal the bitcoins, so it must be kept safe like jewels or cash. For example, it must not be typed into any website. Mnemonic phrases are an excellent way of backing up and storing bitcoins and so they are used by almost all well-regarded wallets.
How Does It Work
There is a very simple explanation of how mnemonic phrases are functioning. The wallet software has a wordlist taken from a dictionary, with each word assigned to a number. The mnemonic phrase can be converted to a number which is used as the seed to a deterministic wallet that generates all the key pairs used in the wallet.
The English-language wordlist for the BIP39 standard has 2048 words, so if the phrase contained only 12 random words, the number of possible combinations would be 2048^12 = 2^132 and the phrase would have 132 bits of security. However, some of the data in a BIP39 phrase is not random, so the actual security of a 12-word BIP39 mnemonic phrase is only 128 bits. This is approximately the same strength as all Bitcoin private keys, so most experts consider it to be sufficiently secure.
It is not safe to invent your own mnemonic phrase because humans are bad at generating randomness. The best way is to allow the wallet software to generate the phrase which you write down.
Mnemonic Passphrases or Two-Factor Mnemonic Phrases
Mnemonic phrases, like all backups, can store any amount of bitcoins. Because the value of your wallet can be extremely high, many wallets make it possible to encrypt a mnemonic phrase with a password. It is like an additional protection of your keys.
The password can be used to create a two-factor mnemonic phrase where both “something you have” plus “something you know” is required to unlock the bitcoins.
This works by the wallet creating a mnemonic phrase and asking the user for a password. Then both the mnemonic phrase and extra word are required to recover the wallet. Electrum and some other wallets call the passphrase a “seed extension”, “mnemonic extension” or “13th/25th word”. The BIP39 standard defines a way of passphrase-protecting a mnemonic seed. A similar scheme is also used in the Electrum standard. If a passphrase is not present, an empty string “” is used instead.
Electrum uses the seed, which is a random phrase that is used to generate your private keys.
For instance:
| slim sugar lizard predict state cute awkward asset inform blood civil sugar |
Your wallet can be entirely recovered from its seed. To use this feature, just select the “restore wallet” option in the startup of the wallet application.
It is not possible to recover your password. However, you can restore your wallet from its seed phrase and choose a new password. If you lose both your password and your seed, there is no way to recover your money. This is why Electrum asks you to save your seed phrase on paper.
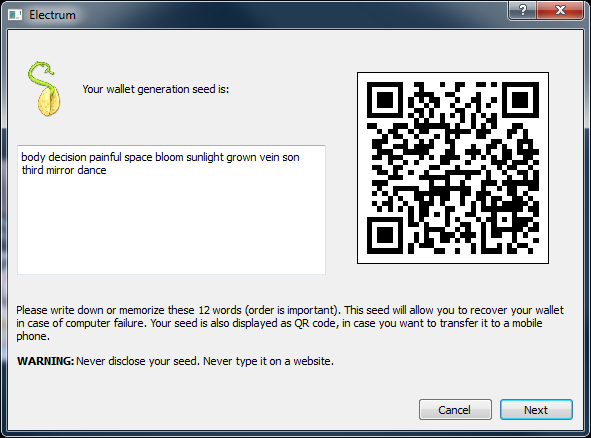
To restore your wallet from its seed phrase, create a new wallet, select the type, choose “I already have a seed” and proceed to input your seed phrase.
As simple as that.
Concerns on the Mnemonic Phrases
Paul Puey, CEO and Founder of Edge, believes that showing the keys on the screen of your mobile device or if you have to type it in, represents major security issue and here is why.
Apparently, Paul sat down with John McAfee, lifelong hacker and former founder of popular anti-virus software, and they discussed securing Bitcoin. Being buried in the hacker community, John sees the biggest threat to our devices as two things, and Paul agrees:
– Keyloggers
– Screen capture malware
Both Android and iOS now allow custom keyboards and it’s entirely possible one of those is snooping your keys and sending them to a malicious party.
With a 12–24 word seed backup, we’ve guaranteed that we’ve given attackers our private key on a silver platter. Show the words on screen and boom, a screen capture virus has it. Have the user enter it to verify the backup (many wallets do this) and bam, a key logger has you “pawned”!
Some wallets talk about being uber secure because they use the Secure Element to store keys in hardware on the phone. But show the keys on screen or have the user type it in and all that hardware security is moot.
So what is the solution? According to Paul, we need a more familiar and still secure way to protect against those top 2 forms of malware. The key is to never show the user their own keys. Never display it on screen. Never have them type it in. But instead encrypt it with a separate set of credentials such as a strong password, and then back it up, behind the scenes, with 2FA to protect it. If a key logger or screen grabber saw your encryption password, they still don’t have the encrypted data to decrypt it. It would require a whole new attack vector to get the data itself.
Final Words
Keeping your wallet secure is one of the most important things if you are planning to deal with cryptocurrencies. It is only your responsibility and there are many ways to increase your protection and security.
No security solution is perfect and it’s not a linear scale of less secure to more secure. It’s about which attack vector you’re concerned about.
There are great solutions available on the market, such as hardware wallets but at the same time they require some initial investment. When it comes to security of your funds, the value at risk is significant.