There is an ongoing arms race in the tech security industry. The bad guys find another way to exploit the system and the good guys try to patch up the leak. It’s not necessarily a bad thing. It’s how security tech advances, and it drives the cryptography industry. The latest onslaught is more subtle and will not directly result in someone emptying your crypto wallet, but it’s worth being aware of it.
You may have heard recently about dusting attacks, but what are they? Why are they a problem, and how can we defend against them?
What you'll learn 👉
What is a dusting attack?
Dust refers to the small quantities of crypto left in your wallet after a trade. These frustrating remnants are impossible to move as the transaction fees are more than the amount being transferred. In the case of Bitcoin, anything under 5000 satoshis is regarded as dust. This equates to about $2 at today’s rate.
The villain sends small amounts of crypto to thousands of wallets and uses chain analysis to track what happens to these funds next. They can see where they are being sent and establish connections with other wallets they are monitoring.
Once enough common links can be established between groups of wallets, it becomes easier to figure out who owns which wallet. There are already blockchain analysis companies busy creating a map of who likely owns which wallet. Law enforcement and tax authorities have an interest in this too – like I say, all the bad guys!
This is especially a problem if you move your dust to a centralized exchange that associates your wallet addresses with your KYC information. (Know you Customer) If you have ever advertised a receive address on a website to accept payment, you could also be a target.
What are the risks?
At this stage, the risks are not catastrophic as the attacker cannot access your wallet or the crypto it contains. However, it sets up further attacks which can be serious. If you’re going to steal something from somebody, it pays to know what they have and where they keep it. The business of thieving comes later, but a knowledge of who owns what is invaluable.
Once a gang of crooks has figured out which wallets you control and how much is in them, the main follow-up threats are Social Engineering, Phishing, and Ransomware attacks.
Anonymity vs Pseudonymity
The blockchain is totally transparent and contains an auditable list of all the Bitcoin transactions ever made. The wallet addresses, the time, and the amount are all recorded in the ledger. If you give someone your Bitcoin address to transfer you some funds, they can peer into your wallet and see exactly what you have spent and received since the wallet was created.
The Bitcoin network is anything but anonymous, but the twist is that you do not have to supply any personal data to create a wallet. So yes, we can see into every wallet, but we cannot (easily) connect that wallet to an individual. That is pseudonymity.
How do I protect against a dusting attack?
Whenever you receive small amounts of unsolicited cryptocurrency from someone you don’t know, you should leave it alone. Don’t touch it. Either Just let it sit in your wallet, or delete that address and never use it again. As long as you don’t forward it anywhere, the hackers can’t monitor where it goes, obviously.
The best way to stay as anonymous as possible is to use a newly generated receive address for every transaction. This is not always possible, especially if you are a business taking payment in crypto. It turns managing all your wallet addresses into a logistical nightmare. The risk of misplacing your crypto becomes greater than any risk from the dusting attacks we are trying to protect against.
I was asked whether we would ever run out of Bitcoin wallet addresses. The answer is no. If you estimate 100 billion people using Bitcoin over the next 100 years (12 times as many humans as exist today), they could each have 1,461,501,637,330,900,000,000,000,000,000,000,000 addresses. It’s about a trillion times as many stars exist in the known universe. That should be enough to be getting on with.
Another potential threat concerns smart contracts. Once you click confirm on your DeFi wallet, you are giving access to a smart contract. If you don’t know the provenance of this smart contract, you could be welcoming villains directly into your wallet. Only deal with established ‘Blue Chip’ DeFi companies with a great reputation that have never been hacked.
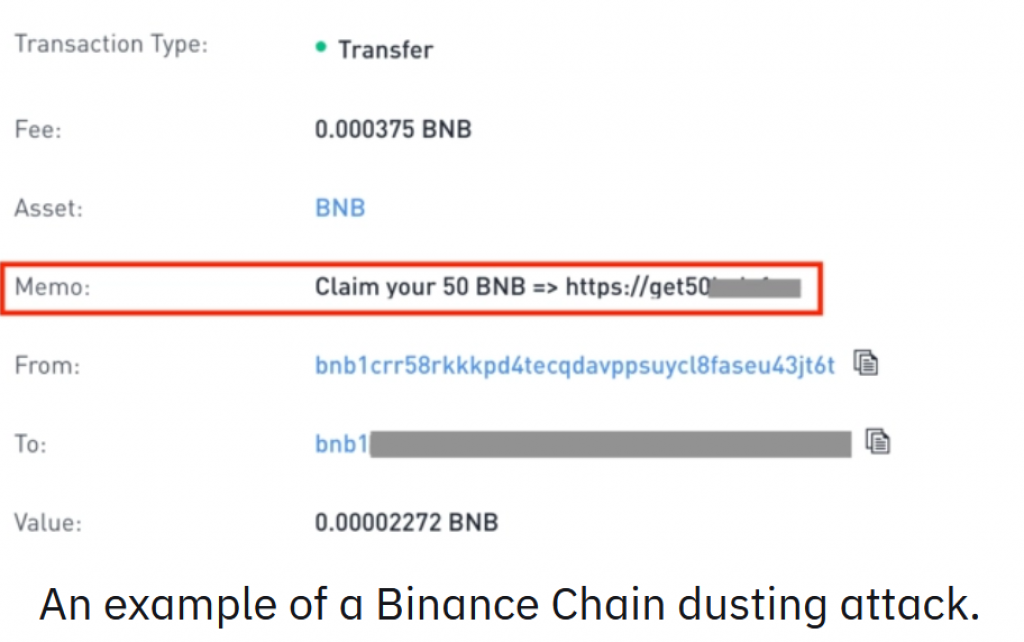
Another recent scam on the Binance Smart Chain included a website address and a message in the notes, telling you about unclaimed crypto you are missing out on. Again, don’t be fooled. Nobody is giving away free crypto. It’s a scam. If you apply regular internet safety rules to crypto, you should avoid these confidence tricksters. The other maxims to remember are, “There’s no such thing as a free lunch,” and, “If it looks too good to be true, then it probably is.”
Confidence tricksters rely on the greed of their victims. Don’t be greedy!
Summary and Thoughts
Most of the threat at the moment comes from subsequent traditional phishing or social engineering attacks. The dusting attacks merely confirm the identity of the target and what can be stolen. This could change, however. Smart contracts are a powerful technology that has not yet been stress-tested in the wild. This makes them super-vulnerable to attacks from bad actors.
Already we have seen malicious code embedded in smart contracts designed to steal from DeFi wallets. The Unlimited Allowance issue has raised questions about the security of DeFi wallets. It’s impossible to know which exploit will be uncovered next, but it’s interesting to note that dusting attacks still require a good old-fashioned social engineering approach to be successful.
In the real world, each potential threat is identified then countered. New threats are engineered and so the process continues. It’s an essential part of the evolution of decentralized blockchain technology. What doesn’t kill us makes us stronger, so we should embrace the challenge and learn from it. It’s how crypto becomes more secure over time.