Update - 2018.04.23
History
The idea of digital cash was born in 1983 in David Chaum’s research paper. He managed to establish an electronic cash company called DigiCash in Amsterdam in order to put his ideas from the research into the real world economy. DigiCash was a form of early electronic payment which required user software in order to withdraw notes from a bank and designate specific encrypted keys before it can be sent to a recipient. This advancement of public and private key cryptography allowed electronic payments to become untraceable by the issuing bank, the government, or a third party. This system of Blind Signatures through DigiCash software improved security for its users through the issuance of secured keys which prevented third parties from accessing personal information through online transactions.

Unfortunately, the DigiCash Company could not continue successfully through the expansion of its user base. Chaum claimed in an interview in 1999 that the DigiCash project, and its technology system, entered the market before e-commerce was fully integrated within the Internet. In 1998, DigiCash filed a bankruptcy and in 2002 the company was sold for assets.
One of the first digital currencies was founded in 1996, called E-gold with underlying instrument in gold. Also there was a popular digital currency called Liberty Reserve, which basically allowed its users convers dollars or euros to Liberty Reserve Dollars or Euros. You were able to exchange them freely with one another at a 1% fee. US government shutt down both currencies as it was reported that they were used for money laundering.
In 2005, commodity based digital currency was used on Tencent QQ’s messaging platform called Q coins or QQ coins. Q coins gained so much popularity that they had negative effect on Chinese Yuan due to the huge amount of speculation.
In 2008, Bitcoin was introduced and it became the most widely used and accepted digital currency.
The Bitcoin was a success due to the fact that it had solved problems which its predecessor could not solve. One of these issues was a double spending. Let’s see how Bitcoin has solved this problem.
Double Spending
Major problem with digital currency was that it could be copied endless number of times and by doing so it loses its purpose and value.
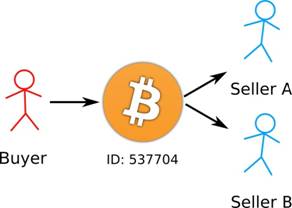
Double spending is the risk that a digital currency can be spent twice. Because Bitcoin is a digital file it is easy to duplicate it, simple copy & paste. So it means that some people may want to make more than one payment with the same Bitcoin that they own.
How does Bitcoin handle double spending issue?
Bitcoin protects against double spending by verifying each transaction added to the shared public ledger or also known as blockchain to ensure that the inputs for the transaction had not previously already been spent. Bitcoin uses a decentralized system, where a consensus among nodes following the same protocol is substituted for a central authority.
For instance, let’s assume you are buying goods from Seller A and you are paying with 1 BTC (we will call this Transaction A). At the same time you are paying to Seller B also 1 BTC (Transaction B). Remember, you only have 1 BTC on your account. Transaction A and Transaction B go to Bitcoin’s unconfirmed transactions pool. The miners pull out Transaction A and it is valid and confirmed since you really have 1 BTC. When they pull out Transaction B it will be invalid as you do not have any more BTC and does not get confirmations. It is simple as that. But what would happen if both of these transactions were pulled out at the same time? Due to large number of miners this could easily happen. Both transactions A and B will show that there is indeed money required. Both of the transactions will be included on the blockchain and the one which gets more confirmations faster will win or in other words get confirmed. It is almost impossible that two transactions get several confirmations at the same time and that is why it is recommended to wait at least 6 confirmations before considering transaction complete. There is no way of knowing which transaction will be completed and which will get canceled.
When the transaction is added to the Bitcoin network, it may be included in a block that is published to the network. When that happens it is said that the transaction has been mined at a depth of 1 block. With each subsequent block that is found, the number of blocks deep is increased by one.
The most of Bitcoin users will consider transaction unconfirmed until it gets 6 blocks deep or 6 confirmations. Sellers and exchanges who accept Bitcoins as mean of payment can set their own required number of blocks needed before funds are considered confirmed. The transactions become more irreversible as the number of confirmations rises, meaning that to be able to double spend that coin, the sender has to go back and reverse all transactions in the 6 blocks that have been added after their transaction, which is computationally impossible.
The sole incident on double spending was in November 2013, when it was discovered that the GHash.io mining pool appeared to be engaging in repeated payment fraud against BetCoin Dice, a gambling site. Dice sites use one transaction per bet and don’t wait for confirmations. GHash.io claimed they had investigated and found an employee who had been doing the double spending and was eventually fired. However, no evidence supporting this was provided and the incident left a permanent cloud hanging over the pool. Regardless, it didn’t seem to hurt their market share much: most miners probably never heard about the incident at all.
Attack Vectors
It is possible for double spending attacks to happen, let’s see how.
Race Attack
There are traders and sellers who accept transactions on „0 / unconfirmed“. By doing so they are exposed to risk that transactions can be reversed. A user can trick the seller by sending a direct payment to the seller and at the same time send the same amount to his own address. Both transactions will go to unconfirmed pool. If the second transaction gets first 6 confirmations the first transaction will be canceled. That is why sellers should wait 6 confirmations before accepting a payment.
Finney Attack
Again the traders or sellers who accept transactions on 0 / unconfirmed are exposed to this type of attack. The attack can happen even with all precautions taken by the seller, because it includes the participation of a miner. But there has to be a specific chain of events. The attack is very complicated to be carried out and it is viable only if profits from attack are massive. Again, the traders and sellers accepting the unconfirmed transactions should consider the cost / benefit of such method.
Vector76 Attack
It is a combination of the Race Attack and the Finney Attack, where transaction with one confirmation can still be reversed. Vector76 Attack is also called a one-confirmation attack. Traders and sellers can protect them by disabling incoming connections and only connecting to well-connected nodes.
It is important to note, that a successful attack costs the attacker one block – they need to ‘sacrifice’ a block by not broadcasting it, and instead relaying it only to the attacked node.
Brute Force Attack

In order to conduct this attack, the attacker needs to have a high hashrate and risks significant expense in wasted electricity.
After the attacker sends a transaction to the seller, he starts privately mining an alternative blockchain fork in which potential double spending transaction is included. The seller, after he sees n confirmations, sends the product. But if the attacker manages to find more than n confirmations at this point, he releases his fork and regains his coins.
If the attack fails, it means that attacker has spent a lot of electricity and the transaction to the seller will be completed and legal.
The success rate of the attack can be even calculated. For example, if the attacker controls 10% of the network hashrate but the merchant waits for 6 confirmations, the success probability is on the order of 0.1%. Because of the opportunity cost of this attack, it is only game-theory possible if the Bitcoin amount traded is comparable to the block reward (but note that an attacking miner can attempt a brute force attack against several counterparties at once).
Majority Attack
It is also called a 51% attack or >50% attack. The name comes from the fact that the attacker needs to control more than 50% of the network hashrate. If that is the case, the Brute Force Attack has a probability of 100% success. As the attacker controls more than 50% of the hashrate it means he can generate blocks faster than the rest of the network.
It does not matter how many confirmations the sellers gets, but it does increase the cost of performing the attack and can make it unprofitable. Delaying the transaction could lead to changes in hashrate.
Security model employed by Bitcoin ensures that no group of miners can control more than half of the hashrate. A miner or group of miners with more than 50% hashrate is incentivized to reduce their mining power and reframe from attacking in order for their mining equipment and Bitcoin income to retain its value.
Conclusion
All Bitcoin transactions must be recorded in the shared public ledger, also known as blockchain, without exception. The method ensures that the user spending coins is the real owner and it prevents double spending and other types of scams. To double spend you will need a massive amount of hashrate or computing power.
There have been many attacks on Bitcoin by different methods but with limited success. The incidents around Bitcoin do not include double spending (except for few rumors), but most of the Bitcoin thefts occurred due to low security level of users under the attack.
You should not be worried about above stated attacks, but should invest more time and money into securing your coins with latest software and hardware wallets.