Bitcoin had its own version of “coordinator” called the checkpoints. The checkpoints are hard coded into the standard client. The concept is, that the standard client will accept all transactions up to the checkpoint as valid and irreversible. If anyone tries to fork the blockchain starting from a block before the checkpoint, the client will not accept the fork. This makes those blocks “set in stone”.
What you'll learn 👉
IOTA centralization problem
As Eric Wall, former author on bitcoin.com, explains in his notorious post on IOTA, the IOTA ledger is constructed as a tree, where the root node (“node” here simply refers to a position in the tree — has nothing to do will network nodes) is the equivalent to the “genesis block”, and every subsequent transaction creates a new node in the tree. From the genesis node, all iotas that will ever be created were distributed to a group of addresses participating in the original ICO in 2015. For a person to extend this tree, his transaction must point to two randomly chosen previous transactions in the tree, and include a tiny Proof-of-Work hash. This creates an ever-growing tree representing the ledger.
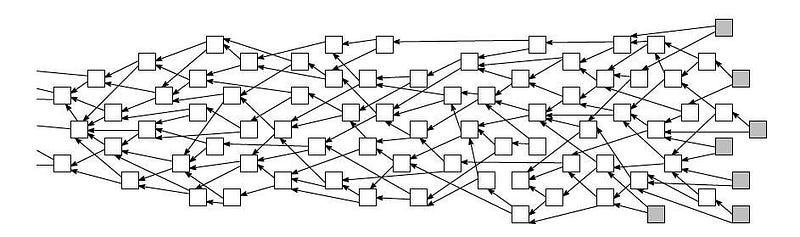
When he has selected the two previous transactions, he also verifies them by making sure they also include the required Proof-of-Work and that they neither directly nor indirectly extend what would constitute a double-spending transaction in the tree.
To choose which branch of the tree to extend upon, he follows a specific MCMC-based algorithm, and as long as the majority of the other users follows the same algorithm, the tree will diverge into the same direction as a result. This direction is then secured over time through the extension of more tiny Proofs-of-Works added by each new transaction. Further, the system only provides any security guarantees in the case that an attacker does not amass more than 33% of the hashpower of the network.
The problem
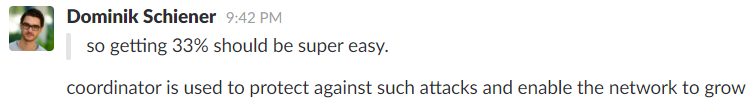
The problem comes down to this; at the current stage, an attacker could very easily amass 33% of the hashpower of the network, because hashing only happens at the instants when new transactions are being added to the tree, and is completed in a second using a normal laptop.
Without the COOs protection, IOTA would be a juicy target destroy. With only 100 IOTA hashes per second securing the network, that means that an individual would only need to maintain a sustained 34 hashes per second in order to completely take over the network.
Have a look at the current IOTA price or IOTA price prediction for 2019 & 2020.
I was unable to find any information on how IOTA resolves this seemingly disturbing security issue on their website or in their whitepaper, but I did find the following information in two non-affiliated blogs after a lot of searching:
Milestones: Milestone is a special transaction issued by a special node called Coordinator. The Coordinator is run by Iota Foundation, its main purpose is to protect the network until it grows strong enough to sustain against a large scale attack from those who own GPUs. Milestones set general direction for the tangle growth and do some kind of checkpointing. Transactions (in)directly referenced by milestones are considered as confirmed.
To make sure, I confirmed this with one of their devs on Slack:
This means that IOTA in its current form does not provide any censorship resistance, since the path of the tree is centrally directed through a Coordinator node run by the IOTA Foundation. As such, IOTA is no more decentralized than an Apache Kafka cluster, or Ripple and their Unique Node List. (EDIT: This also opens up IOTA to double-spend attacks from the Coordinator itself, which I submitted an issue about. The issue was closed with no response. 3 months later, I got the explanation from IOTA co-founder that such an attack would be “not rational”, albeit indeed possible.)
A look at the issue from the other side of the aisle
IOTA holders vehemently defend the current setup of IOTA network with a mandatory reminder that IOTA is already working on the solution on how to decentralize the centralized coordinator.
The coordinator only exists to secure against attacks. Further, IOTA works without the coordinator, but it would then be susceptible to attacks. Other cryptocurrencies including BTC and LTC have used something similar to a coordinator by use of “checkpoints” and Bitcoin Cash still utilizes it currently. Finally, IOTA will get faster and scale better once the coordinator is removed as the tangle cannot scale well beyond tens of transactions per second with the coordinator and the current iri.
Sufficient hashpower is only one of three requirements to double spend in IOTA. To double spend, you also need omnipotence (view of the network topology) and omnipresence (connection to a high number of neighbors). The cost of fulfilling these requirements is hard to quantify but certainly raises the cost to attack the network.
There is a coordinator (COO) node run by the IOTA foundation in order to secure the network from 34% attacks specifically. It does not mean the system is centralized by any means since any experienced programmer could just bypass the node entirely when making transactions, and the role of the COO is merely that of protection; it is still being watched by every other node and its influence spectrum over the network is restricted, and thus the system itself technically cannot be considered overcentralized in that manner. The COO will continue to exist until the tangle is mature enough to be able to fully secure itself by itself.
According to the IOTA Foundation, while Coo has served its purpose well, in the interests of the long-term success of the framework, it is necessary to kill it off first of all because at least theoretically it permits the Foundation to choose which transactions receive priority, and also permits the Foundation to freeze suer funds by instructing milestones to ignore transactions involving such funds.
Despite the announcement, for now there exists no firm timeline has been given for the removal of Coo. A quote from the blog post reads:
“The short answer is that the Coordinator can and will be removed when our research team is satisfied that we understand the coordinator-free Tangle sufficiently.”
The more transactions, the safer the network
The most important thing that needs to occur to remove the COO, is that the native measurement of transactions per second (which ultimately also measures the hashes per second) need to go drastically up in orders of magnitude.
If the IOTA transaction volume were to increase to 1000 transactions per second, then it would require 340 transactions per second from a malicious actor to compromise the network. In order to complete 340 transactions per second, the attacker would need now need the economic power of 340 * $60,000 to 34% attack the IOTA network.
In this hypothetical scenario, the cost of attacking the IOTA network is $20,400,000. This number is still pretty small, but at least you can see the pattern. IOTA will likely need to hit many-thousand transactions per second before it can be considered secure.
How big of a deal is this?
People should stay fair when assessing and judging crypto projects, using an equal measuring stick for all is the only upright approach. Every project has its own vision of how to get to the decentralization fairyland and IOTA is no different. It’s a dynamic process and decentralization won’t happen before the network is mature enough.